Browse
Popular Products




SHOP BY
POPULAR CATEGORIES
BODY ARMOR & BALLISTICS
TACTICAL GEAR
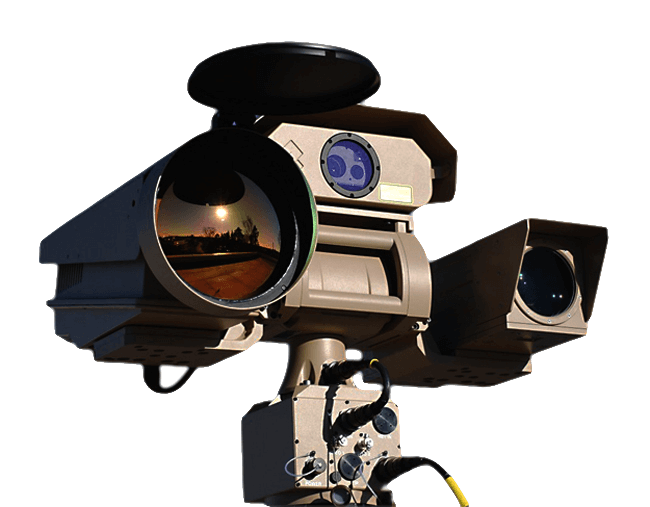
SECURITY SOLUTIONS



Get all the information on our hottest deals and latest security solutions.
Sign up today and receive a special offer.